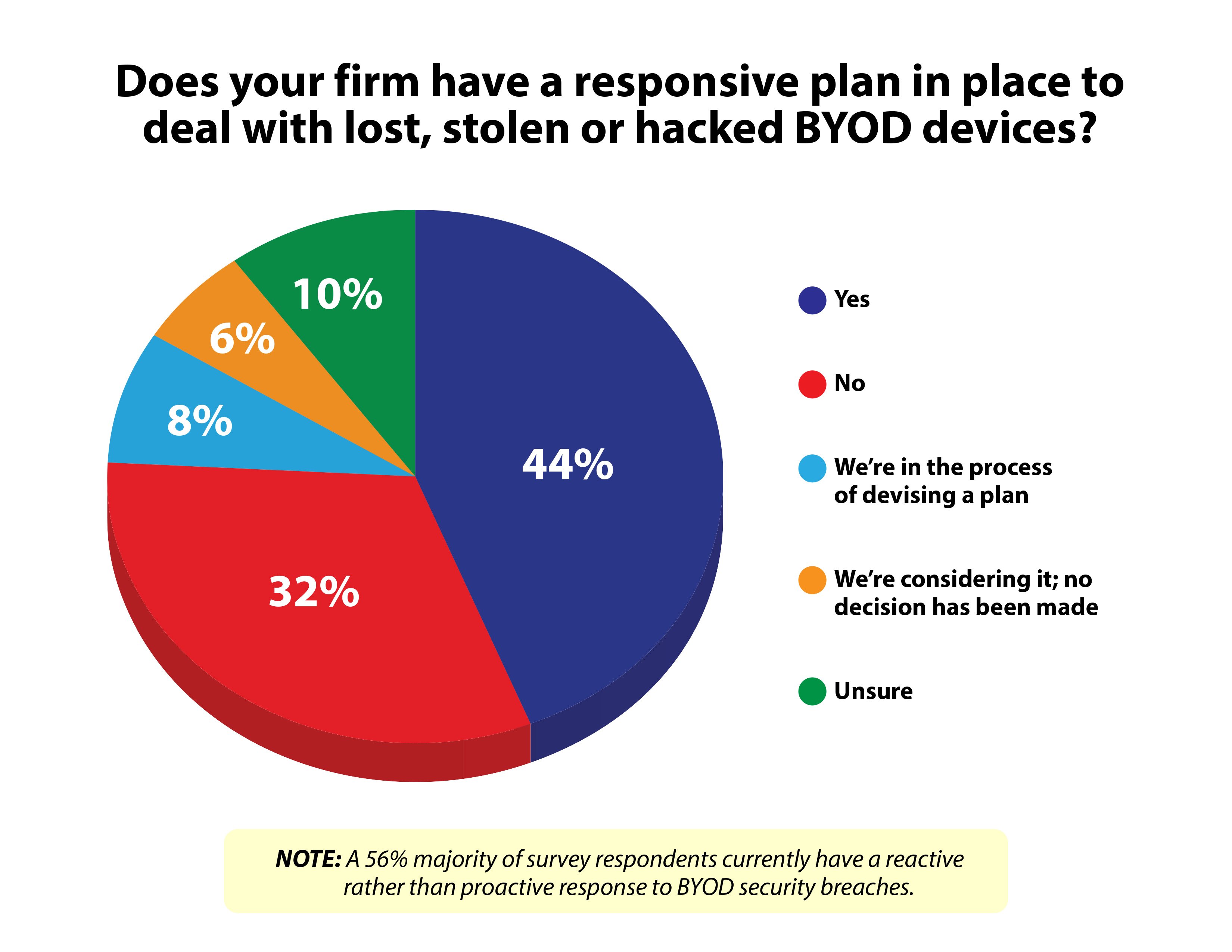
 More than half the organizationsresponding to a new survey said they have no response ready for ahack into data on notebooks, tablets and smartphones their staff isusing as “bring your own devices.”
More than half the organizationsresponding to a new survey said they have no response ready for ahack into data on notebooks, tablets and smartphones their staff isusing as “bring your own devices.”
(Click on the chart at right toexpand.)
|The survey–conducted by Information Technology IntelligenceConsulting and security trainer KnowB4.com– also found that half ofthe respondents concede that BYOD and corporate-owned devices may have beenbreached in the past 12 months without their knowledge, leavingdata and applications alike vulnerable to internal and externalthreats.
|ITIC and KnowBe4 said they drew their conclusions from aFebruary survey conducted online among IT professionals at morethan 300 organizations in 30 vertical market segments including 80%from North America and ranging in size from fewer than 200employees to more than 10,000.
|Along with no knowing they had been breached or having a planfor dealing with problems from personal devices, ITIC and KnowBe4said, “56% of organizations acknowledge they are not fortifyingtheir existing security measures, taking extra precautions orimplementing security training despite recent high-profile securityattacks against Fortune 1000 firms like Adobe, Reuters, Target,Skype, Snapchat and others.”
|Other survey highlights:
- 34% of the participants acknowledged they either “have no wayof knowing” or “do not require” end users to inform them ofsecurity issues with employee-owned BYOD.
- Three in 10 respondents were unaware or unable to discernwhether BYOD security breaches impacted servers, mission criticalapps or network operations.
- 32% said they either have no BYOD-specific security in place ordon't know.
Recommendations from the report–titled “2014 State of CorporateServer, Desktop and BYOD Security Trends Survey”“–include:
- Conduct regular security audits and vulnerabilitytesting. Include server hardware, server OS, applicationand network infrastructure to identify vulnerabilities and comparesecurity across platforms.
- Regularly review and update policies andprocedures. Corporations should review and update theirsecurity policies annually at a minimum or as needed to addressemerging technologies and trends like BYOD and mobility.
- Perform due diligence. Become familiar withall specifics of the platform before beginning any new technologydeployment (such as server hardware, application software,virtualization and cloud deployments.)
- Ensure compliance. The ability to adhere tocompliance standards and meet service-level agreements hinges onserver security, reliability and uptime.
- Estimate the cost of downtime. “Being able toaffix a monetary cost to a security breach and assess the potentialrisk and damages that ensue in the wake of a security breach, willmake the most cogent and compelling case for strong securitymechanisms and security awareness training,” ITIC and KnowBe4said.
Want to continue reading?
Become a Free PropertyCasualty360 Digital Reader
Your access to unlimited PropertyCasualty360 content isn’t changing.
Once you are an ALM digital member, you’ll receive:
- All PropertyCasualty360.com news coverage, best practices, and in-depth analysis.
- Educational webcasts, resources from industry leaders, and informative newsletters.
- Other award-winning websites including BenefitsPRO.com and ThinkAdvisor.com.
Already have an account? Sign In
© 2024 ALM Global, LLC, All Rights Reserved. Request academic re-use from www.copyright.com. All other uses, submit a request to [email protected]. For more information visit Asset & Logo Licensing.