The WannaCry attack is evidence of a meaningful evolution in ransomware, which has strategic implications on cyber attack patterns and, subsequently, insurance coverages and aggregation risk.
There are several motivations at play for cyber attackers, but the greatest and most influential incentive is making money — and using ransomware to block access to enterprise computer systems until a payment is made is proving more fruitful for hackers than targeting private data records. It also means that businesses who have no data records are no longer a lower hazard group.
The evolution of ransomware
Ransomware started to gain meaningful traction in 2013 with the introduction of encryption malware like Cryptolocker, which targeted PCs mostly through phishing campaigns. It was only a matter of time until hackers discovered how to extend ransomware to other types of attacks or asset takeovers.
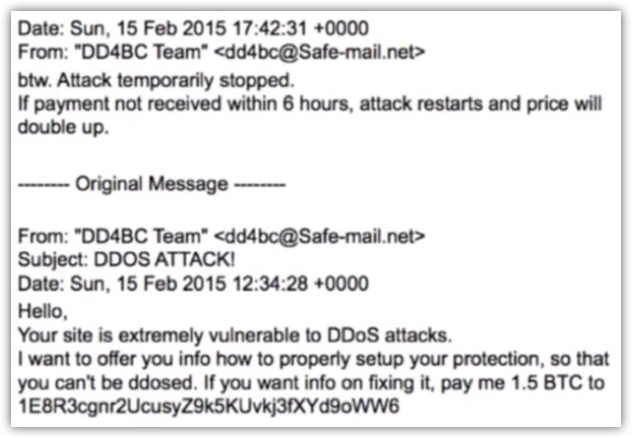
In 2015, we saw the rise and fall of the hacker group DDoS for Bitcoin (DD4BC) who, as their name suggests, requested ransom money to sustain from DDoSing a website. (See image at right for an example of a ransomware e-mail from DD4BC; click image for full resolution.)
The group was arrested in January 2016 by Europol, but the cat was out of the bag: There is big money to be made by attacking enterprise assets. DDoS is not an easily scalable attack, so attackers started considering other ways to deliver large-scale ransom attacks.
Meanwhile, endpoint ransomware has spread like wildfire. In fact, in 2016 approximately half of all organizations reported a ransomware event in the previous 12 months, paying about $1billion in extortion fees. However, risk managers and security experts historically have not been concerned. To date, the financial damage has been relatively small, and the malware used to infect computers was no different than existing botnet malware with a constant, and relatively low, rate of infection. There was no single vulnerability exploit that triggered a mass event. Yet.

Although there has not been an example of catastrophic portfolio loss based on mass exploit of a single vulnerability, it's not enough to reassure smart underwriters. (Photo: Shutterstock)
Aggregation nightmares becoming a reality
Single events that trigger multiple claims, like earthquakes, are relatively straightforward to identify and circumvent in an insurance agreement, such as limiting the definition of computer systems to exclude or limit shared cloud systems. The tougher question, however, has been the possibility of a mass attack based on a single vulnerability in a ubiquitous system.
For example, if most companies have a Windows operating system, and Windows has a vulnerability, an attacker could breach all businesses simultaneously. There is no way an insurance agreement can get around this issue. Although there has not been an example of catastrophic portfolio loss based on mass exploit of a single vulnerability, it is not enough to reassure smart underwriters.
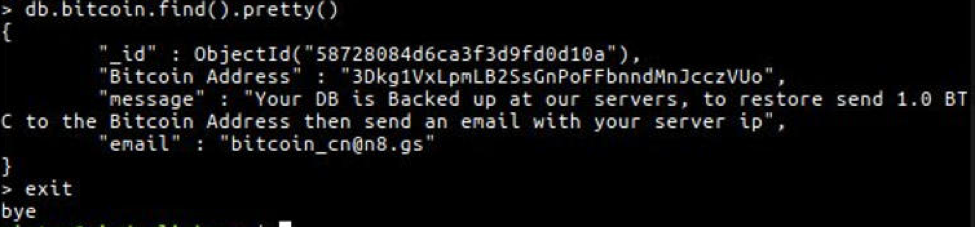
In January 2017, CyberJack's research team detected and analyzed a coordinated attack on MongoDB, a specific type of database provider, exploiting a vulnerability in its latest version. This is huge.
An example from CyberJack of the MongoDB attack. Click image for full resoltuion.
Attackers were systematically going after companies with MongoDB technology and encrypting their databases for ransom, and they had a short window of time in which to do this. Once security researchers discovered the attack, MongoDB pushed out an update and closed the attack window. In a matter of five days, 27,000 databases were hit — over 25 percent of all MongoDB instances worldwide.
In essence, what happened was one of the first meaningful cases of multiple events triggered by a single vulnerability in a coordinated attack.

WannaCry is the biggest case to date of a "single vulnerability = multiple events" aggregation risk. (Photo: Shutterstock)
WannaCry signals a new era in extortion
Which brings us to last week. WannaCry is not a sophisticated ransomware — in fact, it is a similar endpoint encryption malware that we've seen for the last three years. What makes it special is that it utilizes an incredibly powerful and sophisticated vulnerability, weaponized by the NSA and leaked by the hacker group Shadow Brokers. Even though the leak happened almost three months ago — and Microsoft has since released a patch to fix the vulnerability — it's obvious by the sheer size of the attack that many companies did not install the update on all relevant machines. The attack also serves as a grim reminder of how many people click on generic phishing and spam links.
WannaCry is the biggest case to date of a "single vulnerability = multiple events" aggregation risk. It marks a new era in extortion, one which will feature mass events based on a single shared vulnerability, targeting internet facing business assets — not only endpoints, but also web applications and databases.

Ransomware is the first major, large-scale manifestation of business interruption risk. (Photo: Shutterstock)
What does this mean to insurers?
I believe ransomware will be the first major, large-scale manifestation of business interruption risk. This will come from sophisticated ransom campaigns targeting internal assets and configurations, and not endpoint encryption malware like we see today.
With this in mind, insurers are expected to face a set of difficult questions:
- What should be the adequate policy wording and linkage between business interruption, network attack and extortion coverages? Take a peril-specific coverage approach to extortion. Currently, damages triggered by an extortion event are covered under multiple insurance agreements that have independent limits, retentions and underwriting. Mapping out extortion scenarios and the probability and exposure profiles unique to each one will result in superior and more predictable coverage.
- How can they select good risks over bad risks? Study which extortion scenarios to expect, what the attack vector is, and what correlates with lower probability for that attack vector. Using the MongoDB example, consider testing the version of the applicant's MongoDB, and limit the percent of companies in your portfolio that run on MongoDB. Do the same for all other relevant technologies.
- How can they manage the significant increase in aggregation risk? Diversify on technology assets and configurations; not industries. The industry is a proxy for a type of asset (e.g. Healthcare = PHI record), or technology type (e.g. Retail = Point of Sale system), but what really creates aggregation is the underlying specific technology choices.
- How quickly can they provide a quality response? It's important to streamline triage and early response, and cut through the bureaucracy of deploying an incident response team. Knowing when paying ransoms will restore systems could be a key to cost savings.
In short, the future is about to get more complex and more technical. And no one is going to figure it out for the insurance company — it's up to them to answer the tough questions.
Rotem Iram is the founder and CEO of At-Bay (formerly Cyberjack). Rotem previously served as a managing director and COO in the Cyber Security practice of K2 Intelligence, a global risk management firm focusing on cyber intelligence, cyber defense strategy and incident response. Rotem holds a bachelor's degree in computer engineering from the Hebrew University and an MBA from Harvard Business School.
© Arc, All Rights Reserved. Request academic re-use from www.copyright.com. All other uses, submit a request to TMSalesOperations@arc-network.com. For more information visit Asset & Logo Licensing.