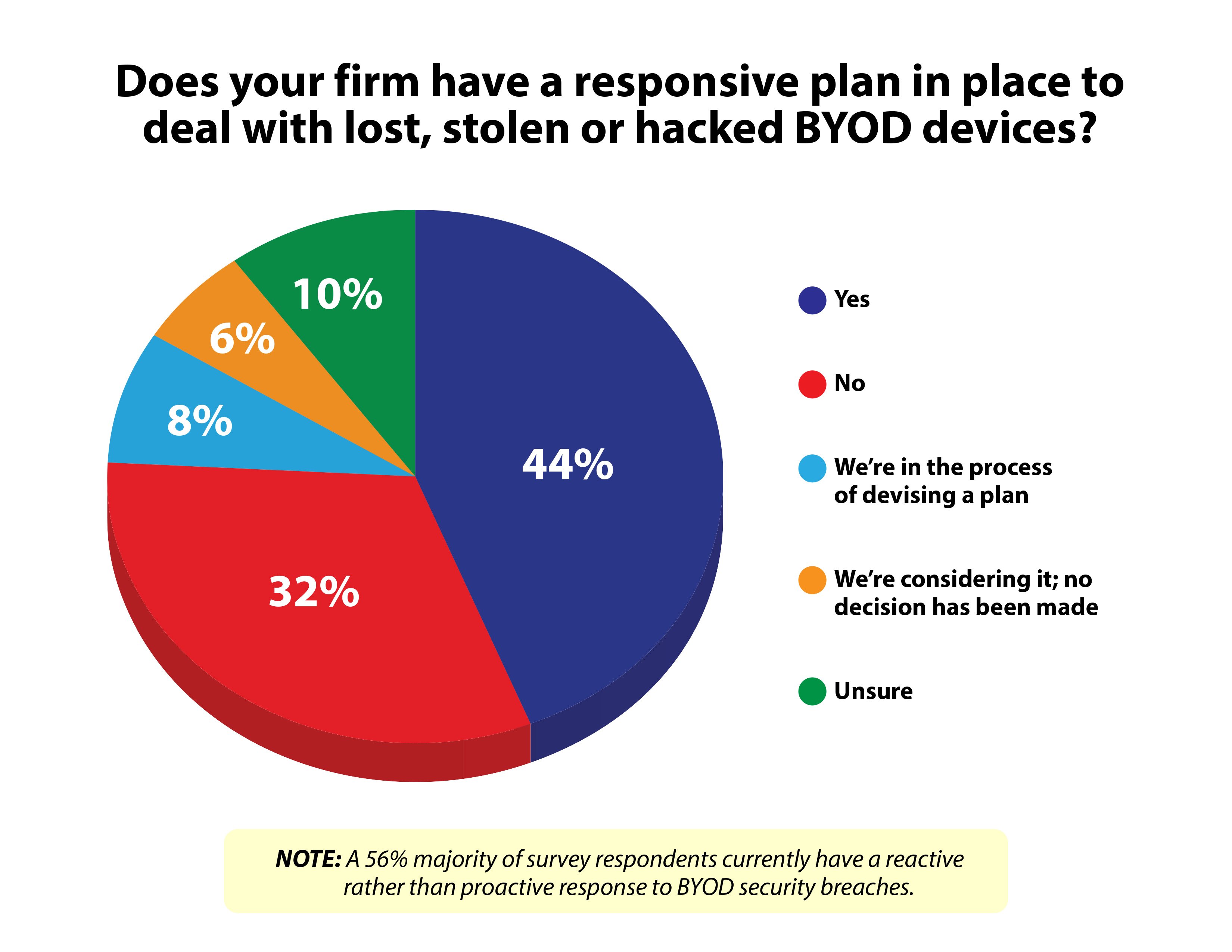
 More than half the organizations responding to a new survey said they have no response ready for a hack into data on notebooks, tablets and smartphones their staff is using as “bring your own devices.”
More than half the organizations responding to a new survey said they have no response ready for a hack into data on notebooks, tablets and smartphones their staff is using as “bring your own devices.”
(Click on the chart at right to expand.)
The survey–conducted by Information Technology Intelligence Consulting and security trainer KnowB4.com– also found that half of the respondents concede that BYOD and corporate-owned devices may have been breached in the past 12 months without their knowledge, leaving data and applications alike vulnerable to internal and external threats.
ITIC and KnowBe4 said they drew their conclusions from a February survey conducted online among IT professionals at more than 300 organizations in 30 vertical market segments including 80% from North America and ranging in size from fewer than 200 employees to more than 10,000.
Along with no knowing they had been breached or having a plan for dealing with problems from personal devices, ITIC and KnowBe4 said, “56% of organizations acknowledge they are not fortifying their existing security measures, taking extra precautions or implementing security training despite recent high-profile security attacks against Fortune 1000 firms like Adobe, Reuters, Target, Skype, Snapchat and others.”
Other survey highlights:
- 34% of the participants acknowledged they either “have no way of knowing” or “do not require” end users to inform them of security issues with employee-owned BYOD.
- Three in 10 respondents were unaware or unable to discern whether BYOD security breaches impacted servers, mission critical apps or network operations.
- 32% said they either have no BYOD-specific security in place or don't know.
Recommendations from the report–titled “2014 State of Corporate Server, Desktop and BYOD Security Trends Survey”“–include:
- Conduct regular security audits and vulnerability testing. Include server hardware, server OS, application and network infrastructure to identify vulnerabilities and compare security across platforms.
- Regularly review and update policies and procedures. Corporations should review and update their security policies annually at a minimum or as needed to address emerging technologies and trends like BYOD and mobility.
- Perform due diligence. Become familiar with all specifics of the platform before beginning any new technology deployment (such as server hardware, application software, virtualization and cloud deployments.)
- Ensure compliance. The ability to adhere to compliance standards and meet service-level agreements hinges on server security, reliability and uptime.
- Estimate the cost of downtime. “Being able to affix a monetary cost to a security breach and assess the potential risk and damages that ensue in the wake of a security breach, will make the most cogent and compelling case for strong security mechanisms and security awareness training,” ITIC and KnowBe4 said.
© Arc, All Rights Reserved. Request academic re-use from www.copyright.com. All other uses, submit a request to TMSalesOperations@arc-network.com. For more information visit Asset & Logo Licensing.